The term digital sovereignty seems to be popping up increasingly on policy agendas and tech discussions around the globe these days. This article is aimed at dissecting what digital sovereignty means in the 2020s and outlining its crucial role in securing data and privacy.
What Does Data Say about Digital Sovereignty?
According to the Eurobarometer survey in 2023, four out of five Europeans (79%) believe that digital sovereignty should be a priority for the EU in the context of global digital competition. This sentiment is echoed worldwide, reinforcing the global digital autonomy push, as countries strive to take control over their digital footprint.
The staggering figure from the Eurobarometer survey aligns with a growing concern not only at the heart of digital sovereignty but intertwined closely with it – data privacy. The constant exchange of information has led to more than just convenience and efficiency. There is an increasing concern about the safety and privacy of the data that switches hands in the grander scheme of things.
The Eurobarometer survey results reflect the increased consciousness and concern among Europeans regarding this matter, showing an increasing global trend. It is safe to say, then, that data privacy, once a secondary concern, has now become a primary matter of concern in the 2020s, and its importance only seems to be amplifying with each passing year.
Looking at another important survey conducted by IDC, since the beginning of the Russia-Ukraine War in February 2022, 75% of European organizations now prioritize digital sovereignty. Companies are adapting to the current situation by either modifying their operations or revamping their IT strategies.
The following results provide evidence of the Sovereignty Stack when asked about actions taken due to concerns about digital sovereignty.

Digital Sovereignty – A Critical Concern
The major concerns centering around digital sovereignty are essentially intertwined with data privacy. There is an increasing concern for the safety and privacy of the data that constantly exchanges hands in the grander scheme.
Key Concerns Related to Digital Sovereignty
- Data Privacy
- Safety of transferred data
- Digital footprint control
Data privacy, once a secondary concern, has become a primary matter of concern in the 2020s, which is being continually amplified with each passing year.
Digital Sovereignty – A Global Trend
Data protection and privacy have emerged as critical concerns under Digital Sovereignty. As stated in Statista, up to 85% of countries have adopted at least one data protection law in 2021, reflecting a global focus on securing data.
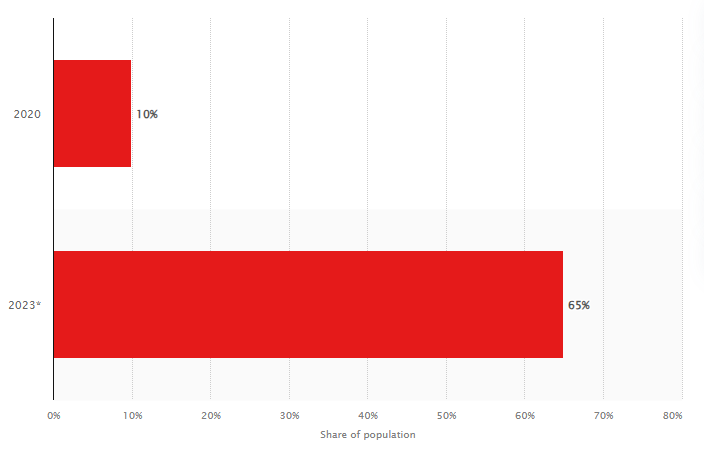
This chart from Statista vividly illustrates the uptick in the proportion of the global population whose personal data is safeguarded under contemporary privacy regulations from 2020 to 2023.
For instance, the EU set a significant benchmark with the adoption of the General Data Protection Regulation (GDPR), which has empowered individuals with control over their personal data. Further East, India embarked on its ambitious Digital India program, aiming to digitally empower its society.
Worldwide Regulations and Legislation
Various regions and countries have taken significant steps to strengthen their data privacy measures. Let’s explore some recent data privacy regulations enacted around the globe:
- General Data Protection Regulation (GDPR), European Union: Implemented in May 2018, GDPR is probably the most robust and well-known data protection framework globally. It sets obligations around user consent, rights to data portability, the right to be forgotten, and severe penalties for breaches, thereby providing individuals with firm control over their personal data. Since it is applicable not only to EU companies but also to any organization dealing with EU residents’ data, GDPR has set a global precedent for other countries to follow.
- California Consumer Privacy Act (CCPA), United States: This state-specific legislation was enacted in California in 2020. As one of the strictest privacy bills in the US, the CCPA gives Californian consumers the right to know what personal data companies are collecting on them, the purpose of its use, and with whom they share it. They also have the right to opt out of the sale of such information.
- Lei Geral de Proteção de Dados (LGPD), Brazil: Brazil’s counterpart to GDPR, the LGPD, came into effect in August 2020. It applies to all businesses and organizations involved in Brazil’s data processing, irrespective of their location. Besides similar rights to GDPR, like data access, correction, and deletion, the LGPD uniquely requires organizations to appoint a data protection officer.
- Personal Data Protection Act (PDPA), Singapore: The PDPA was enacted in Singapore in 2012 but underwent significant amendments in November 2020. The revamped PDPA imposes a mandatory data breach notification and financial penalties for non-compliance. It also includes stringent requirements for data consent, collection, and usage.
- Personal Information Protection Bill, India: Though not yet enacted till now, India’s Personal Information Protection Bill is worth mentioning. The proposed bill is India’s GDPR variation, aiming to regulate the processing of individuals’ personal data and ensure that Indian citizens have the right to privacy.
These initiatives underline the importance of data privacy globally. With tech advances and growing data usage, it is anticipated that many more countries will strengthen their data privacy regulations, reflecting the broader movement toward digital sovereignty.
| Sets obligations around user consent, data portability, and right to be forgotten; applies globally to organizations dealing with EU residents’ data. | Year | Region | Additional Information |
|---|---|---|---|
| General Data Protection Regulation (GDPR) | 2018 | European Union | Brazil’s GDPR counterpart; which applies to all businesses in Brazil, requires a data protection officer. |
| California Consumer Privacy Act (CCPA) | 2020 | United States | Gives Californian consumers the right to know collected data, and opt-out of data sales. |
| Lei Geral de Proteção de Dados (LGPD) | 2020 | Brazil | Imposes data breach notifications, financial penalties; and strict requirements for data consent, collection, and usage. |
| Personal Data Protection Act (PDPA) | 2012 (amended in 2020) | Singapore | Encompasses regulations similar to GDPR; and emphasizes user consent, data access, and deletion rights. |
| Personal Information Protection Bill | Not enacted yet | India | Awaiting bill aiming to regulate personal data processing, ensuring privacy rights for Indian citizens. |
| Data Protection Act 2018 | 2018 | United Kingdom | Implements GDPR post-Brexit, regulating data protection and privacy. |
| Personal Data Protection Law | 2020 | Mexico | Encompasses regulations similar to GDPR; emphasizes user consent, data access, and deletion rights. |
| Personal Information Protection Law (PIPL) | 2021 | China | Enacted to protect personal information and data, introduces rules on cross-border data transfers and user consent. |
| Personal Information Protection Law (PIPL) | 2022 | Japan | Addresses personal data processing, similar to GDPR; introduces rules for transferring data outside Japan. |
| Personal Data Protection Act | 2019 | Thailand | Focuses on the collection, use, and disclosure of personal data; establishes a personal data protection committee. |
The Crucial Role of Digital Sovereignty in Digital Autonomy
The global cybersecurity market currently stands at over $150 billion, reflecting the gravity given to cybersecurity in the chase for digital sovereignty. National Cybersecurity Approaches, such as those employed by Swedish internet service providers, have fostered trust amongst 69% of the Swedish public, portraying a significant level of digital sovereignty.
With digital sovereignty comes digital autonomy, another critical aspect of the current digital landscape. This need is echoed by organizations that mostly believe that digital sovereign identity will be vital in their industries in the future.
Steps Towards Digital Sovereignty / Autonomy
Digital autonomy in the 2020s, while paramount, comes with its challenges. A survey by the World Economic Forum reports that 91% of executives expect new regulations aimed at breaking up data monopolies in the next five years, indicating growing concern over digital sovereignty.
Moreover, data privacy, security, and sovereignty have become potential flashpoints owing to the majority of the world’s data being stored and processed by a handful of large tech companies. However, many countries have initiated strategies to tackle these concerns, such as France, where 96% of citizens emphasize it is essential to affirm digital sovereignty.
Emphasizing the importance of utilizing on-premises data centers or private clouds instead of relying heavily on hyper-scale cloud providers is also crucial in the discourse of digital sovereignty. Breaking free from dependence on a few dominant tech companies for data needs is not only beneficial for bolstering data sovereignty but also mitigates risks associated with data breaches or misuse. On-premises data centers or private clouds offer an added layer of protection as they give organizations full control over their data. In addition, they enable countries and businesses to enforce their own stringent data regulations, thereby solidifying their digital sovereignty status. Thus, moving towards private data storage and management solutions should be a vital part of any strategy aimed at affirming digital sovereignty.
Final Thoughts on Data Privacy
Navigating the current landscape of global digital governance requires an understanding of digital sovereignty and its accompanying components, such as data protection laws and national cybersecurity strategies. With the rise in data breaches, as indicated by the 86% increase in 2022, the call for policies addressing digital sovereignty gets louder.
However, with various global entities working towards digital sovereignty and a rise in regulations aimed at preventing data monopolies, the future of digital sovereignty could bring about a diverse, secure, and inclusive internet landscape. For all things digital sovereignty, stay tuned for more updates and insights.
To dive deeper into how compliance fits into the modern digital sovereignty narrative, read Understanding Modern Compliance Challenges in the Data Privacy Era
