In today’s digital landscape, creating a truly private workplace is essential to safeguard what matters most—your organization’s sensitive data, communications, and business continuity. As remote work becomes the norm and cyber threats escalate, IT leaders and business owners face unprecedented challenges in protecting confidential information and ensuring regulatory compliance. This article is designed for IT decision-makers, business owners, and security-conscious professionals who want to understand the risks of remote work, the importance of private workplaces, the evolving regulatory landscape, and practical solutions to secure their operations.
What Is a Private Workplace?
A private workplace refers to a dedicated, secure environment—such as a private office, suite, or digital workspace—designed to enhance concentration, confidentiality, and productivity. Private workplaces, such as dedicated offices or private suites, provide improved concentration, enhanced confidentiality, and reduced distractions, which drive productivity. They offer a private, secure environment for handling sensitive company data, documents, and private discussions. By creating clear boundaries between personal life and professional responsibilities, private workspaces support employee well-being and foster a quiet, controlled, and customizable environment that aids in separating work from home life. This foundational context is crucial for organizations seeking to protect sensitive information and maintain operational integrity in a distributed work environment.
Article Overview
In this article, we will explore the sobering reality of remote work data breaches, examine why remote workers take risks, and analyze the limitations of public collaboration tools. We will discuss the benefits and features of private workplaces, review the regulatory requirements that organizations must meet, and present actionable data protection strategies. Finally, we will introduce Carbonio as a secure, private solution for email collaboration and data security.
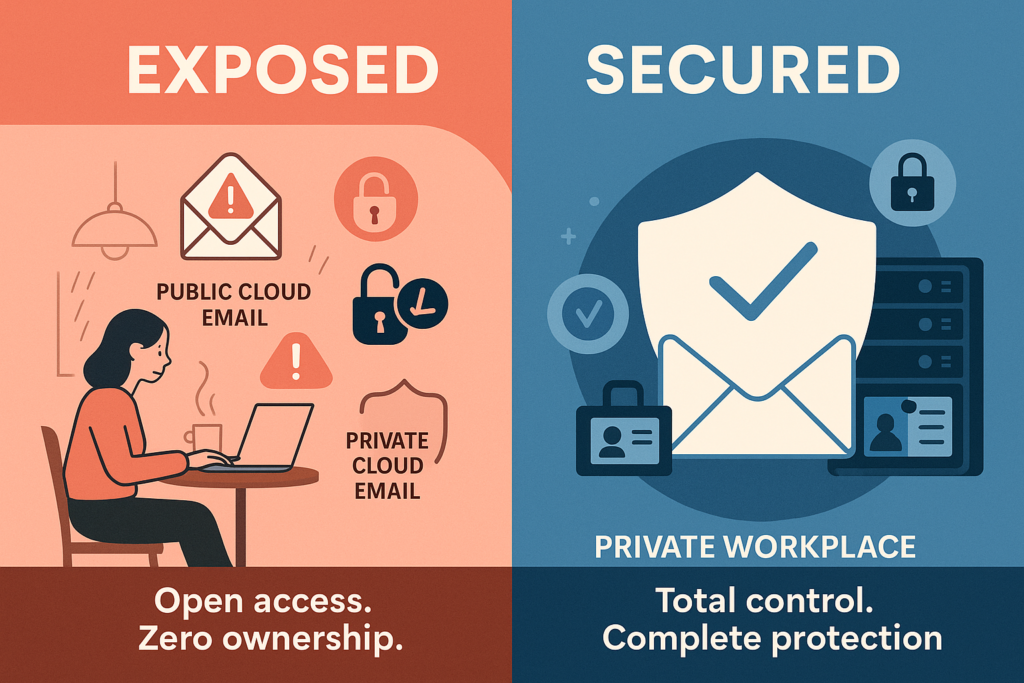
Email is no longer just a tool—it’s your organization’s most targeted vulnerability. As remote work expands, inboxes are accessed from everywhere, often on unsecured devices. With 89% of remote workers falling for phishing and cyberattacks surging 700%, relying on public cloud email is no longer just risky—it’s negligent.
So why trust critical/sensitive communication to platforms you don’t fully control? In the context of a private workplace, this question becomes even more urgent.
The Benefits and Features of a Private Workplace
Private workplaces, such as dedicated offices or private suites, provide improved concentration, enhanced confidentiality, and reduced distractions, which drive productivity. These environments are specifically designed to minimize interruptions and visual distractions that are common in open-plan settings, allowing employees to focus deeply on their tasks. Private workplaces offer a private, secure environment for handling sensitive company data, documents, and private discussions, making them ideal for organizations that prioritize data security and confidentiality. Additionally, private workspaces create clear boundaries between personal life and professional responsibilities, supporting employee well-being by providing a quiet, controlled, and customizable environment that aids in separating work from home life.
The Sobering Reality of Remote Work Data Breaches
Hybrid work was meant to empower people. But for many IT teams, it did something else entirely: it opened the floodgates to risk. No longer confined to secure office networks, employees now access their inboxes from homes, airports, and personal devices—creating new vulnerabilities by the hour. This shift puts critical data at greater risk, as essential business information is now more exposed outside traditional security perimeters.
Nearly 9 out of 10 remote workers fall for phishing attempts (Proofpoint), and remote users are three times more likely to be targeted than their in-office peers. Even worse, 30% admit to bypassing company security protocols deliberately (Fortinet). The result? VPN usage has plummeted by 43% (CrowdStrike), and half of all organizations have reported a rise in breaches due to remote work (Netwrix). These vulnerabilities have led to a significant increase in data theft, as attackers exploit weak points to steal sensitive and critical information.
Add to this the human element: overworked IT teams, confused users, and a workplace culture that increasingly blurs the lines between personal convenience and corporate risk. In fact, more than half of employees admit to taking riskier actions when working remotely (Tessian). Your email system—once secured by firewalls and on-premises protections—is now exposed, fragmented, and under constant threat. And unless you’re the one in control, it’s not a question of if, but when.
As these risks mount, organizations must consider how private workplaces can help mitigate vulnerabilities and restore control.
The Human Element: Why Remote Workers Take Risks
What drives this risky behavior? Tessian’s comprehensive survey reveals that 52% of employees deliberately take greater security risks while working remotely than they would in an office environment. This risk-taking manifests in multiple ways:
- 54% regularly use personal devices for confidential work, according to Symantec’s Internet Security Threat Report
- 41% use unsecured personal applications to access data and sensitive company information, as found in Wrike’s Remote Work Security Survey
The psychological separation between work and personal space has deteriorated, leading to dangerous security shortcuts – Forbes.
Understanding these behaviors is crucial for developing effective strategies that reinforce the boundaries and security benefits provided by private workplaces.
The Collaboration Tool Crisis
Public email tools promise access. But do they give you the authority to protect what matters most?
In practice, many organizations find they’ve traded oversight for convenience. A Symantec study surveyed 3,000 workers across several European countries and found that over half (53%) of employees use their personal devices for work when outside the workplace, which includes checking work email. Nearly as many—41%—use unsecured personal apps to access sensitive files every single day (Wrike).
Public platforms often lack the ability to restrict access to sensitive data, increasing the risk of unauthorized exposure and making it difficult to meet regulatory or national security requirements.
Meanwhile, cyberattacks have surged by an alarming 700%, with email and collaboration tools among the top targets (Check Point).
These tools may serve the masses well, but they were never built for industries where compliance, auditability, and data sovereignty are non-negotiable.
So ask yourself: If your sector demands trust and accountability, can you really afford to settle for platforms you don’t control?
This growing reliance on public platforms highlights the urgent need for more secure, private alternatives.
The Shift Toward Private, Sovereign Control and General Data Protection Regulation
According to Puredome’s 2024 report, 71% of enterprise leaders are moving to private or sovereign cloud platforms—a powerful signal that organizations want control, not compromise (Puredome).
Private email collaboration platforms let you:
- Host secure email, calendars, and file sharing on your terms
- Retain full control over encryption, data residency, and user access
- Align with zero-trust architectures and policy-based restrictions
- Enable forensic logging and fail-safe compliance
- Ensure data availability even during outages or crises, supporting business continuity
The result? Reduced exposure. Enhanced trust. Complete accountability.
If public platforms leave you vulnerable, sovereign solutions help you reclaim control and eliminate blind spots—driven by the need for a robust data protection strategy.
As organizations recognize these advantages, the transition to private workplaces and sovereign solutions becomes a strategic imperative for long-term security and compliance.
Data Protection Regulations: Navigating the Legal Landscape
In today’s digital workplace, data protection regulations are way more than just legal requirements—they’re the absolute foundation of trust, accountability, and operational resilience that your business desperately needs! As your organization handles increasing volumes of sensitive data, the stakes for compliance have never been higher, and you simply can’t afford to ignore them.
The General Data Protection Regulation (GDPR) stands as a global benchmark for data protection that you need to take seriously. If your organization collects, stores, or processes the personal data of EU residents, you’re required to uphold strict standards of data privacy, data security, and transparency. Non-compliance can result in severe penalties that could devastate your business, making it absolutely essential for your enterprise to implement robust data protection strategies that safeguard your sensitive data from data breaches and unauthorized access.
In the United States, the Health Insurance Portability and Accountability Act (HIPAA) sets rigorous standards for protecting health information that you can’t overlook. If you’re a healthcare provider, insurer, or related organization, you must ensure the confidentiality and integrity of protected health information (PHI) by deploying advanced data protection tools and access controls to prevent data loss and unauthorized disclosure. The Accountability Act’s requirements extend to every single aspect of your data management, from secure storage to responsible data use and disclosure.
The California Consumer Privacy Act (CCPA) further expands the landscape of data protection laws in ways that directly impact your business operations! This regulation grants California residents unprecedented rights over their personal data that you need to respect. If your organization is subject to the CCPA, you must enable individuals to access, delete, or opt out of the sale of their data, and you’ll face significant consequences for failing to protect sensitive information.
Beyond these headline regulations, a host of other data protection regulations—such as the Financial Services Modernization Act, Payment Card Industry Data Security Standard (PCI-DSS), and the Video Privacy Protection Act—underscore just how critical data security and data privacy are across industries. Each regulation brings its own set of requirements for data discovery, classification, and loss prevention, demanding a proactive approach to compliance that you simply cannot postpone.
As mobile devices become ubiquitous in your business operations, mobile data protection has emerged as a critical concern that deserves your immediate attention. You must address the unique risks posed by mobile data access, ensuring that your data security measures extend beyond on-premises data centers to every single endpoint. Effective data lifecycle management is equally vital for your organization, encompassing the entire information lifecycle from data collection and storage to secure disposal.
To navigate this complex regulatory environment successfully, you must adopt comprehensive data protection strategies that actually work! This includes deploying advanced data protection tools, enforcing granular access controls, encrypting data at rest and in transit, and conducting regular data discovery and classification exercises. Data loss prevention solutions and information lifecycle management practices are absolutely essential to protect your enterprise data, maintain data integrity, and ensure compliance with evolving data protection trends.
Ultimately, staying ahead of data protection regulation gdpr and other data protection regulations is not just about avoiding penalties—it’s about building a resilient, trustworthy organization that you can be proud of! Your business can confidently protect sensitive data, support business continuity, and foster lasting stakeholder trust that will set you apart from your competition.
With these regulatory demands in mind, organizations must implement practical strategies to build a truly private workplace that meets both security and compliance requirements.
Building a Truly Private Workplace with Data Protection Strategies
Creating a secure remote work environment requires a comprehensive approach that addresses both technical and human factors. Organizations must consider the following strategies:
Robust Authentication and Access Management
- Robust Authentication: Implement robust authentication systems and access management that verify user identity through multiple factors and enforce role-based access controls.
Least-Privilege Access Controls
- Strict Access Controls: Establish strict access controls that enforce least-privilege principles.
End-to-End Encryption
- End-to-End Encryption: Deploy end-to-end encryption for all sensitive communications.
Data Protection Solutions
- Data Protection Solutions: Deploy data protection solutions such as encryption, data loss prevention (DLP), and backup tools to safeguard sensitive information and ensure operational continuity.
Security Awareness Training
- Security Awareness Training: Conduct regular security awareness training tailored to remote work scenarios as part of ongoing data protection efforts, including fostering a security-aware culture among staff.
Private Collaboration Platforms
- Private Collaboration Platforms: Adopt private collaboration platforms that keep data within organizational boundaries.
This final element—private collaboration platforms—has emerged as the critical missing piece for many organizations struggling with remote security challenges. By integrating these strategies, organizations can create a private workplace that not only protects sensitive data but also supports productivity and compliance.
Meet Carbonio: Private Email Collaboration and Data Security You Control
This is where Zextras Carbonio enters the picture—not as another cloud-based inbox, but as a self-hosted, fully private email and collaboration suite. Designed to meet the demands of security-conscious IT environments, Carbonio gives you total control over your communication infrastructure.
Unlike SaaS giants, Carbonio empowers IT teams to:
- Deploy email, calendars, chat, and file sharing within their own infrastructure
- Enforce SPF, DKIM, DMARC, and TLS policies out of the box
- Integrate with LDAP, SSO, and multi-factor authentication
- Retain Full Data Ownership
- Monitor access, permissions, and sharing—all from a unified admin panel.
- Support automated data inventory and data classification to help organizations organize, secure, and manage sensitive information for compliance and risk management.
Carbonio’s compliance features assist the Data Protection Officer (DPO) in meeting regulatory requirements, conducting audits, and demonstrating accountability to authorities and data subjects.
It’s not just private by design. It’s secure by default, and most importantly, it’s yours.
Instead of trusting your most sensitive communications to a shared, external service, Carbonio empowers your IT team to own the stack—from SMTP to mobile sync. And it does so without compromising usability, making the transition from public cloud platforms seamless for both end users and administrators.
By adopting a solution like Carbonio, organizations can realize the full benefits of a private workplace—combining productivity, confidentiality, and regulatory compliance in one secure platform.
The Strategic Imperative
Data protection encompasses privacy, security, availability, and compliance, making it a foundational element of any private workplace strategy.
The evidence is clear: conventional approaches to remote work security are failing. The statistics cited throughout this article point to an unsustainable situation that demands immediate attention from decision-makers.
The stakes couldn’t be higher. Beyond the immediate financial impact of breaches, organizations face regulatory penalties, litigation, reputational damage, and erosion of customer trust. Data protection is important for safeguarding sensitive information, avoiding financial losses, and maintaining regulatory compliance, which is essential for upholding customer trust and operational continuity. For regulated industries, these consequences can be existential threats.
Personally identifiable information is a critical category of data at risk, requiring specific handling and protection measures to comply with privacy regulations and prevent misuse.
Forward-thinking leaders recognize that secure remote collaboration isn’t merely an IT concern; it’s a strategic business imperative that directly impacts organizational resilience and competitive advantage. Those who act decisively to implement private workplace solutions are positioning their organizations to thrive in an increasingly distributed work environment.
Taking the Next Step
Zextras Carbonio offers an alternative, a way to own your email infrastructure without compromising usability or compliance. It’s more than a tool. It’s a security posture, a compliance strategy, and a business continuity safeguard rolled into one private, self-managed platform.
The question isn’t whether you need secure email collaboration. The real question is: Do you want to control it, or just hope it’s protected?
To read more on how you can protect your business from cyber threats, read this article.
