Does the GDPR require encryption?
The short answer is “no.”
The somewhat longer, more accurate answer is “no, but you might want to consider it, though you have to be aware it won’t guarantee compliance on its own.”
What’s Encryption, Anyway?
Do you remember those times in primary school when you would send ciphered messages to your best friend(s), using an alphabet only you could read?
Encryption is the same concept, made more secure (and less funny) by algorithms.
When using encryption protocols, the information you want to share is translated into a string of random data before being circulated. Only those who have access to the decryption key can make the data revert to their original format – to everyone else, your message, file, or picture will look like a string of numbers.
Encryption types can be further classified depending on how many keys you’re using (symmetric and asymmetric encryption) and who has access to them (end-to-end encryption vs. server-to-user encryption).
Several encryption algorithms are in use, and the level of protection can vary significantly among them.
What Does The GDPR Say About Encryption?
Having clarified what encryption is, we can now answer another question: what does the GDPR say about it?
The (surprising) answer is, “not much.”
The word encryption figures just four times in the whole Regulation: once in the recital and three times in three separate articles. The most important of those is probably Article 32, relating to the “security of proceedings.”
The article in question requires data controllers and data processors to implement “appropriate technical and organizational measures” to ensure that the personal data under their control remains as protected as possible.
Article 32 goes on to list a few measures that might be considered “technically and organizationally” appropriate: the first measure mentioned is “the pseudonymisation and encryption of personal data.”
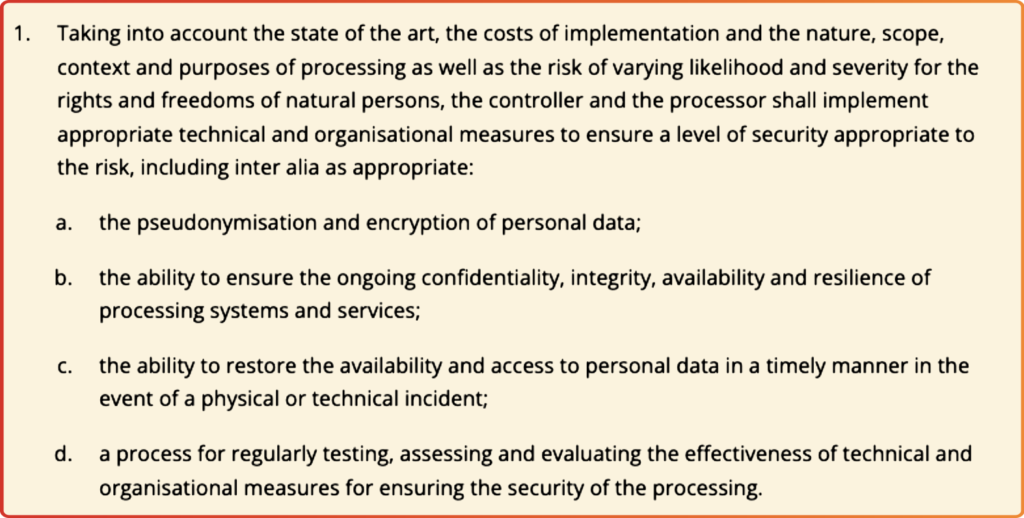
Now, the list provided by Article 32 is neither compulsory nor exhaustive.
On the one hand, data controllers (and processors) are not legally required to implement one or more of the measures listed by the GDPR: what matters is the end result, that is, the safety of the personal data.
So if you can guarantee that the personal data entrusted to you remains secure even without encryption, there’s no obligation to have the data encrypted.
Conversely, however, implementing encryption is not by itself sufficient to guarantee compliance with Article 32.
As we’ve said before, several encryption algorithms are in use, and the level of protection might vary significantly. Therefore, if you choose an encryption protocol that’s not up-to-date or sufficiently robust, you are not adopting “adequate measures” as per Article 32 and are thus violating the GDPR.
Ps. You might be wondering why the GDPR doesn’t offer a definitive list of measures that are considered adequate. The answer is that such an omission is deliberate. Technology evolves way faster than any legislation does. By pointing out only the desired result and leaving data controllers freedom of choice as to how they will achieve it, the Regulation ensures that controllers will always favor state-of-the-art solutions.
GDPR & Encryption: What Should You Do?
Since you are not required to do so by the GDPR, it’s up to you to decide whether you want to encrypt the data entrusted to you. You might find that other solutions work best for you, and that’s ok as long as you can guarantee an appropriate level of security (and demonstrate it).
Having said that, encryption (in particular, encryption supported by a reliable protocol) remains a good, cost-effective solution for protecting personal data.
Using end-to-end encryption when communicating with third parties, for example, ensures that the personal data you might happen to share remains between the two of you. In this case, even the service provider cannot read the content of the message as it doesn’t have access to the decryption key.
So yeah: saying that you could, potentially, do without encryption doesn’t mean that you shouldn’t even consider it.
Quite the opposite: if you use a reliable protocol, encryption does offer an additional layer of security to the personal data you are processing, as it significantly reduces the risk of data breaches.
GDPR & Encryption: Two Caveats
Having established that encryption is a measure worth considering, there are two caveats you should always keep in mind to avoid nasty surprises – and potentially, even nastier fines.
First, encrypted personal data is still personal data as far as the GDPR is concerned.
As we’ve seen, the GDPR assumes that as long as a particular piece of information can be traced back to the natural person to which it refers, it should be treated as personal data. Only when anonymization is permanent can we safely say we’re out of the (data) woods.
Since you, as the data controller, hold the decryption key, the anonymization is always reversible. As a result, the encrypted data always remains personal data, subject to the GDPR provisions.
The second thing to consider is that using encryption doesn’t exempt you from having to observe other GDPR provisions.
To give you a practical example, it doesn’t matter if you use state-of-the-art protocols to encrypt personal data when it was illegally acquired.
It doesn’t matter if you use end-to-end encryption when sharing a piece of information that you couldn’t share in the first place.
And it doesn’t matter if your data processor uses encryption if, for any reason, there’s no contract regulating your relationship with them.
GDPR & Encryption: The Takeaway
Encryption might cover you when the security of personal data against third-party breaches is concerned.
But third-party breaches are just a piece of the GDPR puzzle, so don’t be tempted to believe that you are above board just because you’re using encryption protocols.
Always look for solutions that guarantee you a high level of security – and a high level of data sovereignty.
Do you want to know more about privacy and security?
