In this article, we will discuss e-mail protection and dissect some of the most common strategies applied all over the world by system administrators. We will be following this with more specific articles to show how to apply each strategy on your Carbonio CE servers.
The Problem
With the majority of e-mails being spam on the internet, e-mail providers are always looking for ways to filter unwanted mail. On the other hand, no e-mail provider wants the bad reputation of being a spam sender. Most of the time system administrators have to manually configure strategies to not only fight the large volume of incoming spam but also try to avoid their domain from being recognized as spam sender even by mistake.
There are two main problems when it comes to spoofing, phishing, and spam:
- Endangering users’ data by tricking them to expose their personal information,
- Deteriorating the reputation of your servers and domains over the internet by making them recognized as spammers.
Endangering Users’ Data
Spoofing and phishing are both types of cyber-attacks that attempt to fool users into exposing personal information. Spoofing is a type of identity theft in which a person attempts to use the identity of another genuine user. In contrast, phishing is a phenomenon in which an attacker uses social engineering techniques to gain sensitive and personal information from a user. Spoofing and phishing are real threats endangering your users’ accounts.
Deteriorating Server Reputation
Another threat caused by spammers is causing a bad reputation for your domain or servers. When spammers send forged communications using your organization’s name or domain to perform spoofing or phishing on some users, recipients may wisely recognize them and report them as spam. As a result, genuine correspondence from your servers may also be tagged as spam automatically by the recipient servers deteriorating the internet reputation of your servers over time.
The Solution
The urgent need for a solution to the above problems has led to different e-mail protection strategies being developed. Some of the most common ones include SPF, DKIM, DMARC, and rDNS. Below we will discuss these common strategies.
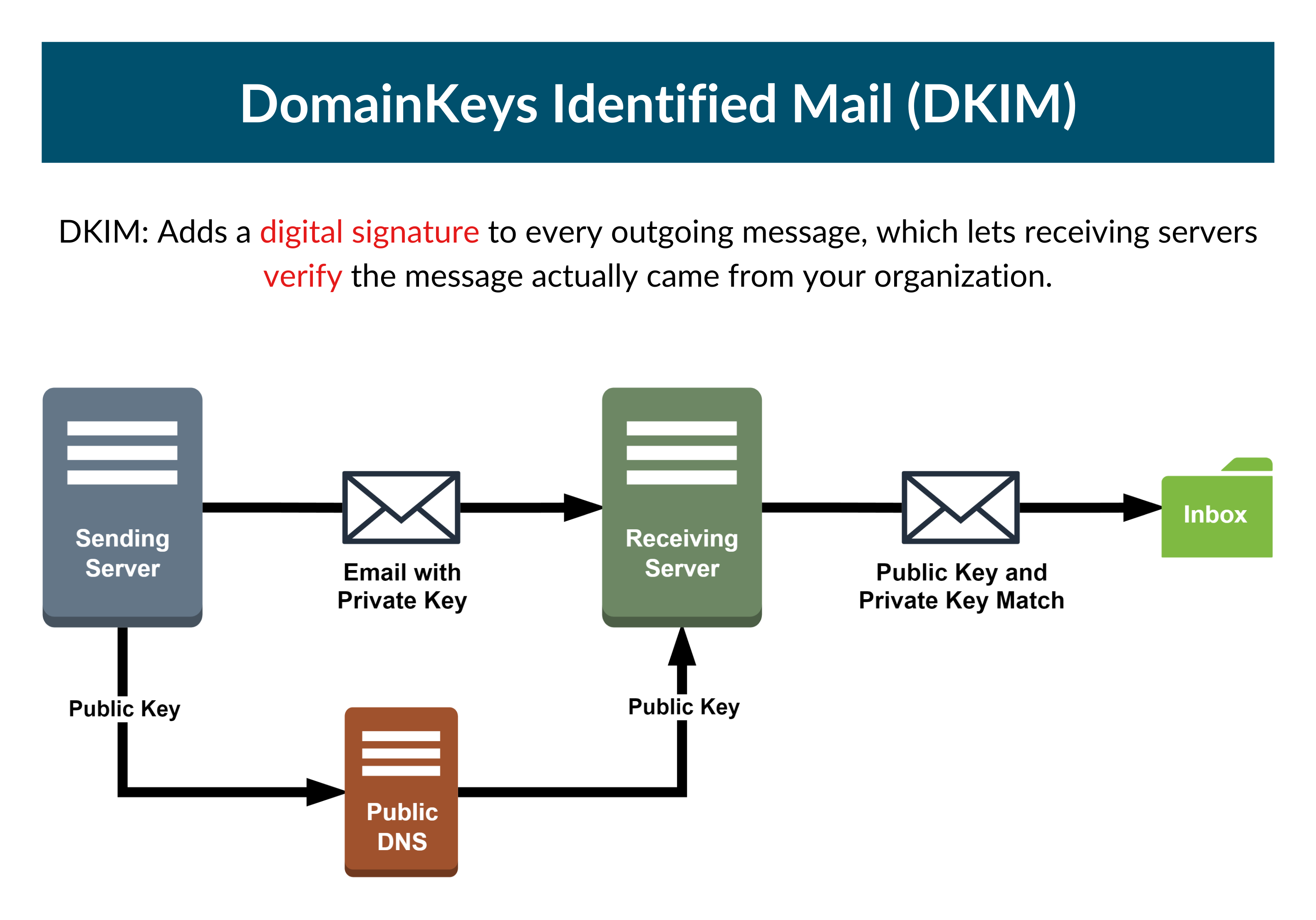
DKIM
DKIM (DomainKeys Identified Mail) is an e-mail protection strategy that allows a domain to accept responsibility for e-mail transmission by signing messages in a way that other providers can verify. DKIM uses cryptographic verification to validate its records in a message.
DKIM was created in 2004 by combining two related efforts: Yahoo’s “improved DomainKeys” and Cisco’s “Identified Internet Mail.” Several IETF standards-track specifications and support papers were developed using this definition, culminating in STD 76, and later in RFC 6376.
Go to Everything You Need to Know about DKIM for Your Carbonio Community Edition Servers to learn how to configure DKIM for your Carbonio CE.
SPF
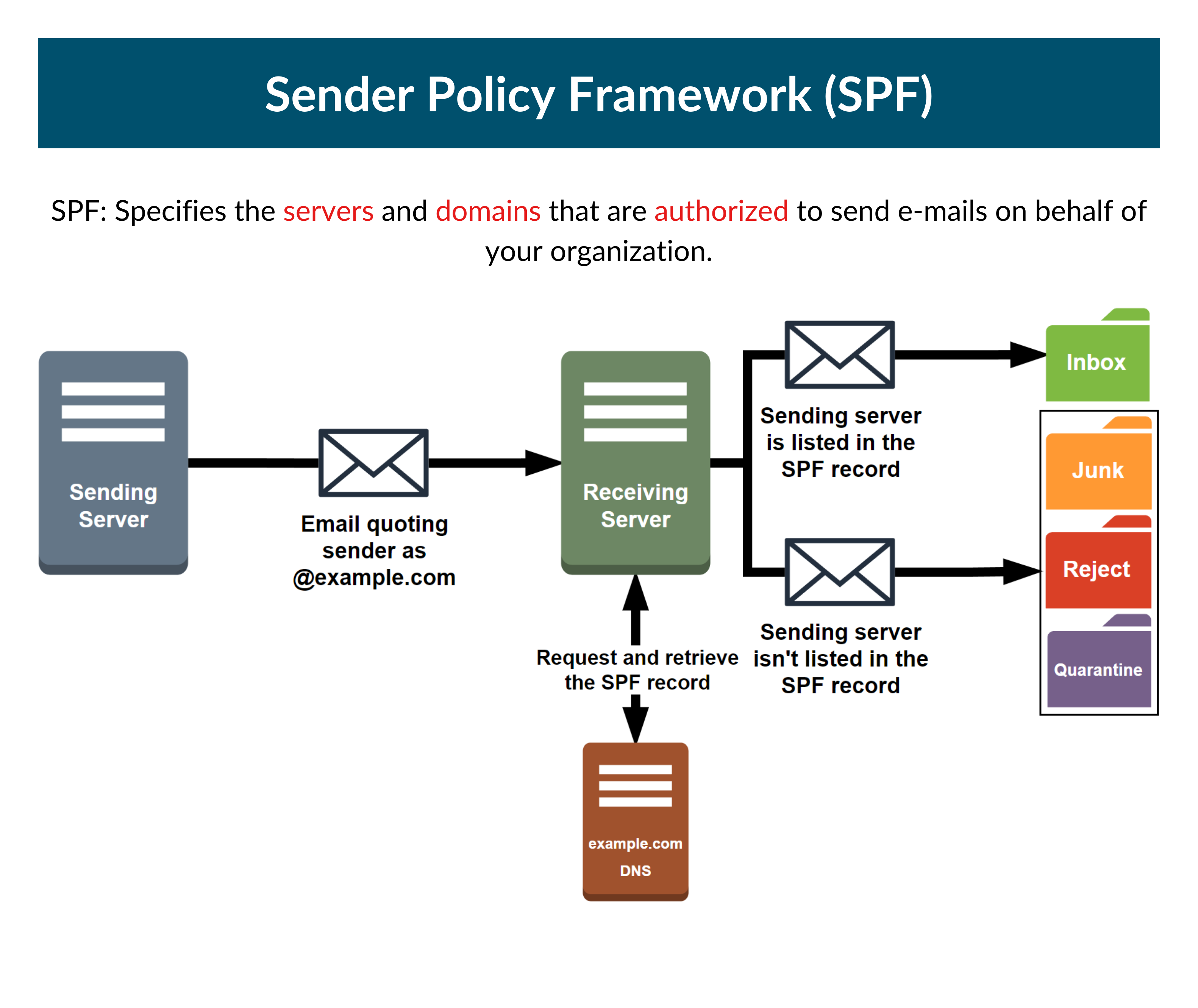
The Sender Policy Framework (SPF) is an e-mail authentication technology that is used to prevent phishing attempts. It enables your firm to select who is authorized to send e-mail on your domain’s behalf. This is essential because, in a typical phishing assault, the threat actor spoofs the sender’s address to make it appear to be an official corporate account or someone the victim knows.
SPF, on its own, is restricted to detecting a falsified sender claim in the e-mail’s envelope, which is employed when the letter is bounced. It can only identify the forging of the visible sender in e-mails (spoofing) when used in conjunction with DMARC.
The first notion of SPF happens somewhere between the years 2000 and 2002. It led to the formation of the IETF Anti-Spam Research Group (ASRG) and its mailing list where it was further developed.
SPF was issued as a “proposed standard” by the IETF in RFC 7208 in April 2014.
Go to Everything You Need to Know about SPF for Your Carbonio Community Edition Servers to learn how to configure SPF for your Carbonio CE.
DMARC
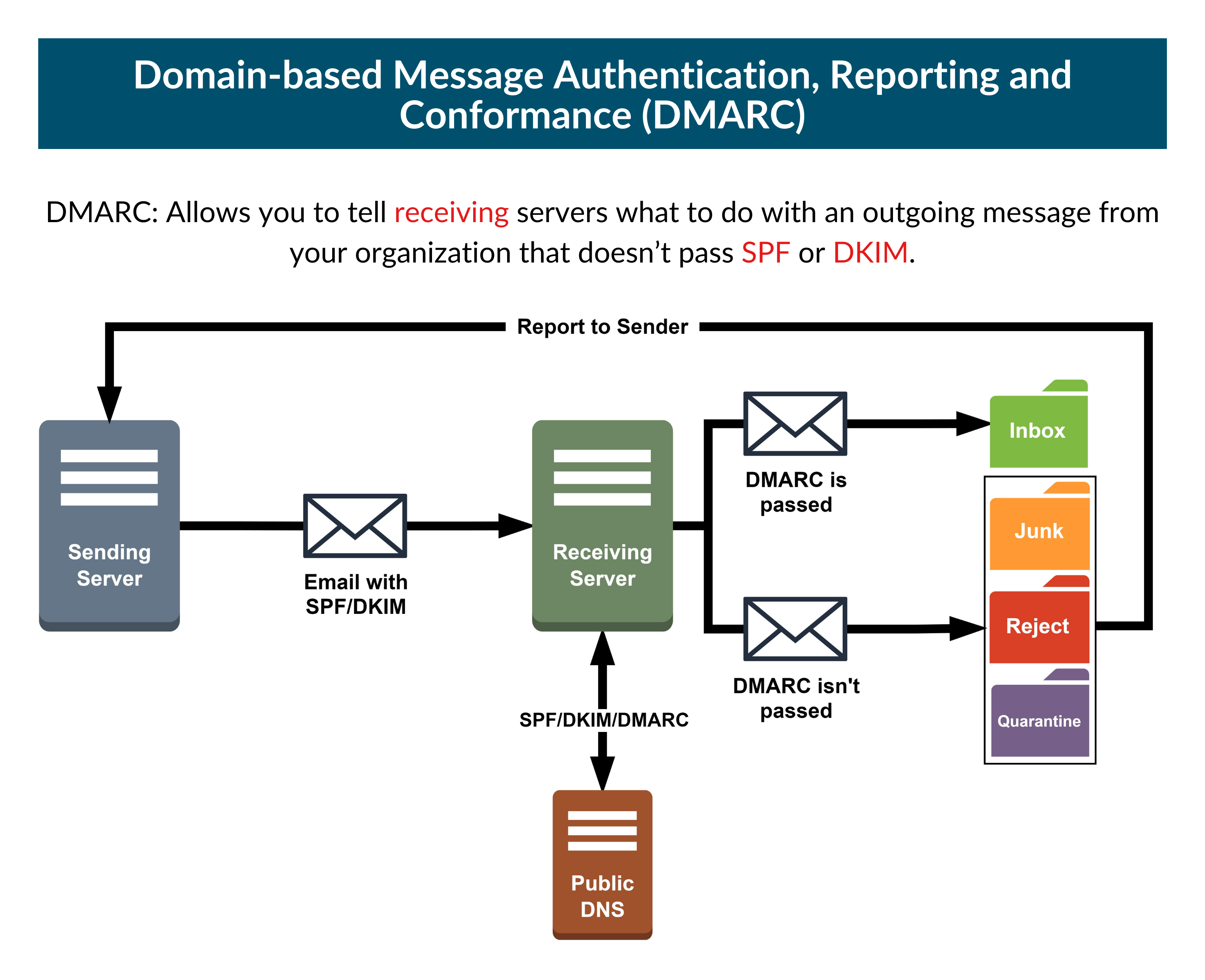
Domain-based Message Authentication, Reporting, and Conformance (DMARC) is a technological definition developed to aid in the reduction of the possibility of e-mail-based abuse. This is done by addressing two long-standing issues with e-mail authentication mechanisms at the operational, implementation, and reporting layers.
It works by establishing a policy within your DNS records that controls whether to send mail from your domain using DKIM, SPF, or both. This enables you to safeguard your domain against phishing e-mails.
A draft of DMARC specifications has been maintained since 30 January 2012 on dmarc.org. In 2014, an IETF working group was created to address DMARC, and its interoperability concerns and produce a revised standard definition and documentation. Meanwhile, the current DMARC standard had achieved an editorial state that was widely accepted and deployed. RFC 7489 was released on the Independent Submission stream in the “Informational” (non-standard) category in March 2015.
Go to Everything You Need to Know about DMARC for Your Carbonio Community Edition Servers to learn how to configure DMARC for your Carbonio CE.
rDNS
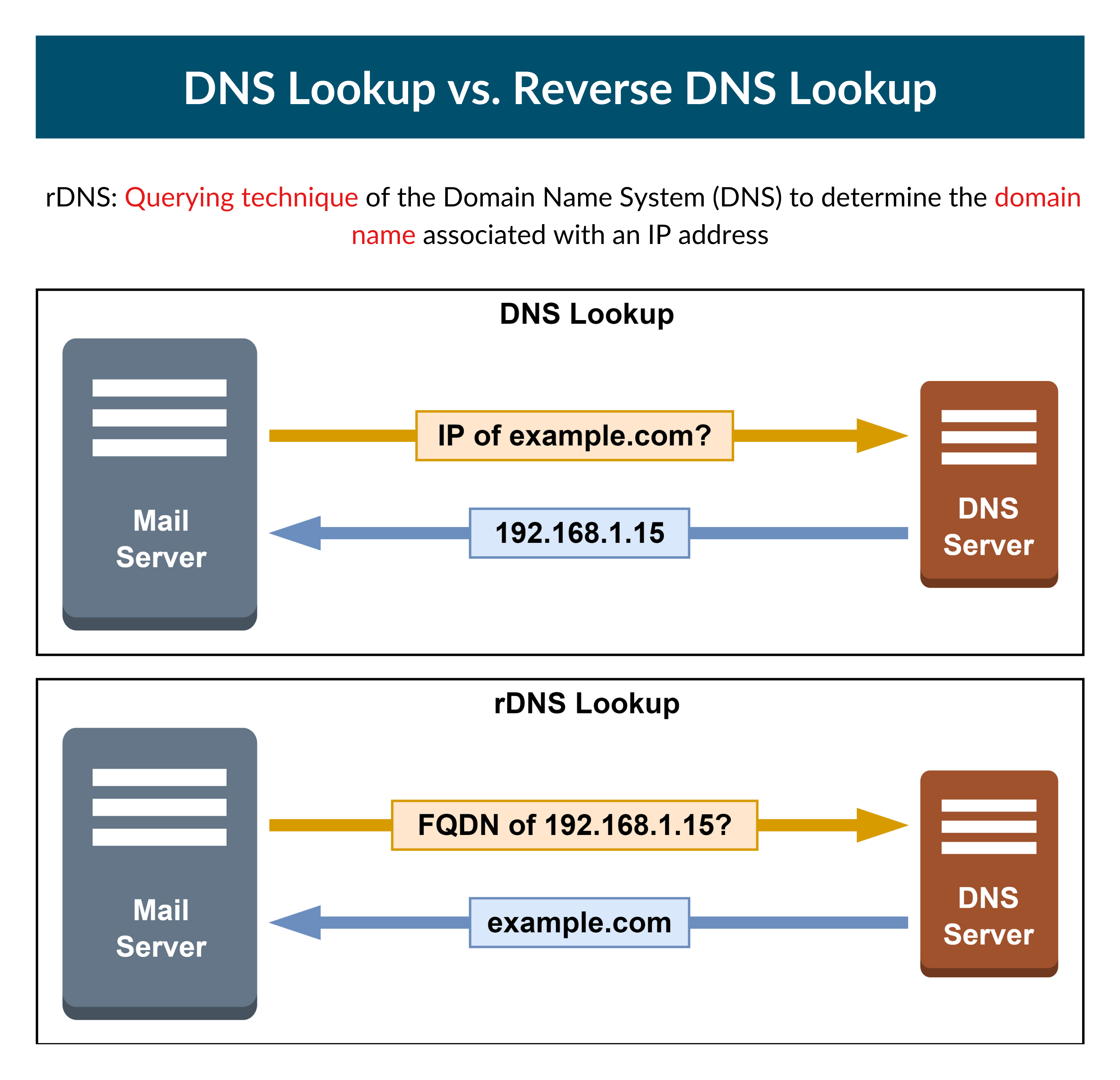
The reverse DNS resolution (rDNS) defines the domain name linked with an IP address. Many e-mail providers will refuse any e-mail that lacks a verified rDNS.
It is a critical procedure and one of the first that administrators do. This is due to both what is indicated in the preceding section and its utility as an anti-spam tool. This is because it allows you to check for dynamically assigned addresses; a practice very rarely done by legitimate mail servers. Such e-mails are marked as spam.
Though rDNS is not an Internet Standard requirement and IP addresses with no reverse entry do exist, the informational RFC 1912 recommends that “every Internet-reachable host should have a name” and “for every IP address, there should be a matching PTR record”.
Go to Everything You Need to Know about RDNS for Your Servers in Carbonio Community Edition to learn how to configure rDNS for your Carbonio CE.
